Security teams are under increased pressure to keep up with the advancing threat landscape. Organizations need help finding the right staff and ensuring they can work effectively.
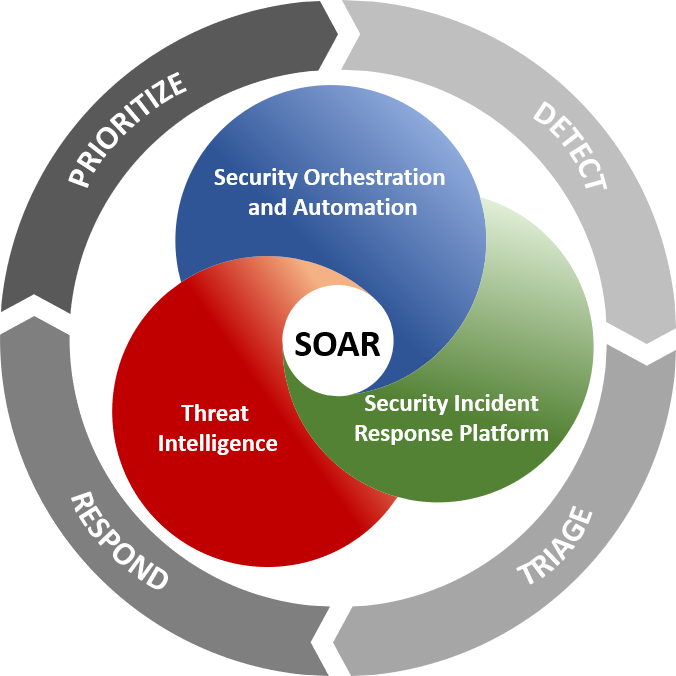
SOAR platforms can alleviate these concerns by aggregating data across various tools and systems. This enhances the context and improves the accuracy of cybersecurity intelligence.
Streamlined Incident Response
SOAR platforms are a technology stack of compatible software programs that enable IT technologists and Cybersecurity professionals to collect data about security threats and vulnerabilities. They also allow IT teams to react to low-level security events without relying on human intervention.
These SOAR platforms automate long manual tasks and manage all aspects of the incident response lifecycle. This increases analyst productivity and reduces errors.
A SOAR system can automatically queue and prioritize alerts, organize them to make them accessible for analysts to understand, and modify the dashboard, so it displays them in the most helpful format to users. Moreover, the platform should provide a big-picture view of all security data so that analysts can quickly make decisions and take action.
Streamlined Incident Response
SOAR solutions can reduce the mean time to detect (MTTD) and mean time to respond (MTTR) by reducing alerts and alleviating alert fatigue. They also improve cybersecurity intelligence by aggregating and analyzing data from different sources, enhancing the context for all cybersecurity threats.
SOAR tools can also automate a significant part of the incident response workflow through procedures known as playbooks. These automated workflows can include blocking firewall or IDS system IP addresses, suspending user accounts, and quarantining infected endpoints. They can also be used to trigger notifications to relevant parties.
Enhanced Threat Intelligence
Security operations teams often rely on various security tools to detect threats and resolve incidents. These tools provide insights into threats and incidents, such as vulnerabilities in the IT infrastructure that cyber attackers could exploit. However, managing all of this data manually can take time and effort.
Security orchestration software helps reduce this reliance on manual incident handling by automating tasks that involve several security tools working together. This can significantly streamline incident response processes for security analysts, enabling them to free up their time to pursue more strategic activities like research and investigations.
A SOAR platform ingests threat alerts from security organizations’ detection tools and executes automated playbooks coordinating actions across enrichment, response, and allied agencies. This enables security teams to view all incident data in a single case management view, adding context to the information and improving operational efficiencies and maturity of the cybersecurity posture over time.
Moreover, SOAR platforms can automatically fetch threat intelligence from global threat databases to add this intelligence to an incident’s information and help security analysts triage the source and target of the attack. Such data enrichment reduces the MTTD (Mean Time to Detect) and MTTR (Mean Time to Respond) and increases the readiness of security operations teams for upcoming attacks.
Enhanced Collaboration
A modern SOAR platform helps security teams connect detection, enrichment, and response tools to deliver a consolidated view of threat intelligence, enabling collaboration and response processes. This is done by automating tasks and providing playbooks that analysts can use to execute responses.
With the increased volume and velocity of cyberattacks, large and small businesses are still seeking resources to secure their networks. They are also facing a cybersecurity skill gap and a cyber talent shortage.
Detecting threats faster, and responding to them more efficiently, is critical to improving cybersecurity outcomes. With enhanced data context from a SOAR solution, security teams can respond to alerts more quickly and reduce the mean time to detect (MTTD) and mean time to respond (MTTR).
Improved data context also allows security teams to prioritize better and investigate alerts. This can help to lower MTTD and MTTR, which reduces the impact of threats on the business.
Additionally, SOAR solutions can help to alleviate alert fatigue and eliminate repetitive, error-prone, and mundane tasks. This frees security team members to focus on more critical tasks and projects.
A clear vision of what SOAR platforms can do for your organization and its goals is essential before embarking on the journey. This will enable you to choose the most appropriate and effective SOAR platform.
Reduced False Positives
False Positives are a significant headache for SOC teams, who often are inundated with bogus alerts that do nothing to help prevent future attacks. This can distract them from focusing on real threats, which could cost organizations much money and time.
Fortunately, there are some ways to reduce the number of false positives that occur within a modern security operation. One is reducing the number of filtering rules incorrectly applied to traffic. Another is by adjusting attack-detection thresholds to minimize FPs.
However, FP reduction techniques must be effective in misuse and anomaly detection. A single error can produce cascading FPs that exacerbate the problem.
As a result, defenders should look for tools that provide feedback and metrics on the FP rates for providers and information sources. This way, they can see what type of errors are occurring and make a more informed decision about how to reduce them.
Another way that SOAR platforms can reduce false positives is by automatically enriching incoming incidents with relevant indicators of compromise. This can be done through various means, including ingesting data from threat intelligence providers and internal knowledge. It can also be done through predefined asset classification or machine-readable business impact analysis results. The resulting insights can be used to identify critical security events that should be prioritized for investigation and remediation.




